Products
Solutions- MFA for Exchange Emails
- MFA for Office 365 Emails
- MFA for AD-Joined Computer Login
- MFA for Entra-Joined Computer Login
- MFA for Entra ID (External MFA)
- MFA for VPN
- MFA for Remote Desktop
- MFA for IIS Websites
- MFA for Cloud Services
- MFA for Office 365
- MFA for NetMotion Mobility
- MFA for Parallels RAS
- Electronic Visit Verification

Authenticators
SaaS
Services
Compliance
Resources
Tools
Multi-Factor Authentication

If you are looking for an on-premises, enterprise grade 2-factor authentication (2FA) or multi-factor authentication (MFA) product that can secure all commonly used business applications and resources, and also provides a wide range of authentication methods, then you are in the right place.
Deepnet DualShield is a multi-factor authentication system that unifies a variety of authentication methods, protocols, solutions and user experience in a single platform. In addition to the MFA functions, DualShield also provides self-service Password Reset, Single Sign-On (SSO), Identity & Access Management (IAM) and Adaptive Authentication. It is one of the most powerful and flexible multi-factor authentication system in the world.
Deepnet DualShield can be installed on-premise or hosted in a private cloud, which means that you will have the total control of your own user authentication system, and that you will be able to keep your users’ identities and credentials in a safe place.
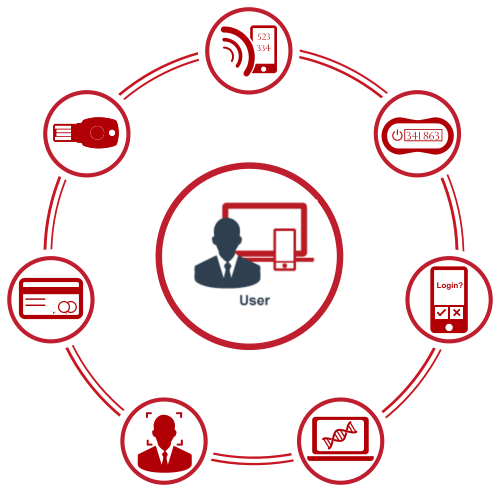
Unified Authentication Methods
DualShield supports almost every type of multi-factor authenticaiton method that you have ever seen and wanted to use, covering all areas in knowledge-based (what you know), token & device based (what you have) and biometrics (what you are).
- OTP (One-Time Password) by SMS, email and voice call
- OOBA (Out of Band Authentication) by push notification, SMS and voice call
- OTP tokens, keyfobs and cards
- OTP apps, e.g. Deepnet MobileID, Google Authenticator etc
- Grid cards, proximity cards and smart cards
- USB keys (FIDO U2F)
- Keystroke Dynamics
- Biometrics, e.g. Fingerprint, Face & Voice recognition
- Device Fingerprint, Device ID, Device DNA.
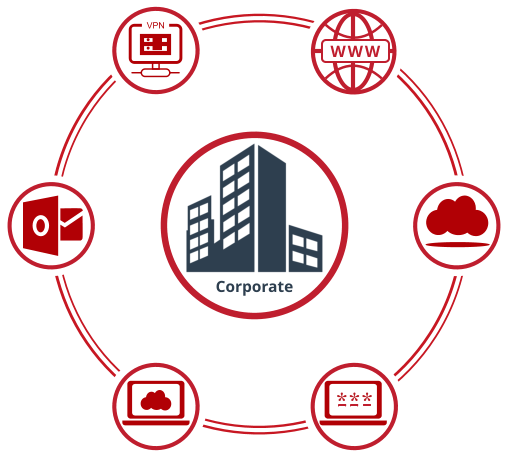
Unified Authentication Solutions
DualShield can secure all commonly used enterprise and web/cloud applications with multi-factor authentication, covering VPN & RDP remote access, Windows, Mac and Linux OS Logon, Web & Cloud services as well as Outlook emails.
- VPN Login, e.g. Cisco ASA, Palo Alto SonicWall. WatchGuard, etc.
- Windows Login: AD domain login, RDP login
- MacOS Login
- Web Applications. e.g. Sharepoint, CRM, ERP, etc
- Cloud Service, e.g. Office 365, Google Apps, SalesForce, AWS, etc.
- Outlook Anywhere, Outlook Web Access, ActiveSync
Unified Authentication Protocols
DualShield supports several authentication protocols that have been used by different types of applications, including LDAP, RADIUS, SAML, FIDO and OATH.
- LDAP: commonly used to provide a directory service for storing user information and to verify user credentials, i.e. usernames and passwords.
- RADIUS: a networking protocol that provides centralized Authentication, Authorization, and Accounting (AAA) services, commonly used by networking devices such as firewalls and VPN servers.
- SAML: an open standard for exchanging authentication and authorization data between parties, in particular, between an identity provider and a service provider. Commonly used by web & cloud applications to provide single sign-on (SSO).
- FIDO: a set of security specifications for strong authentication including multifactor authentication (MFA) and public key cryptography (PKI). Commonly used to replace password with device based authentication.
- OATH: a set of open authentication standards, e.g TOTP (Time-based One-Time Password) and HOTP (Event-based One-Time Password), which have become the de facto OTP standards supported by many multi-factor authentication products.
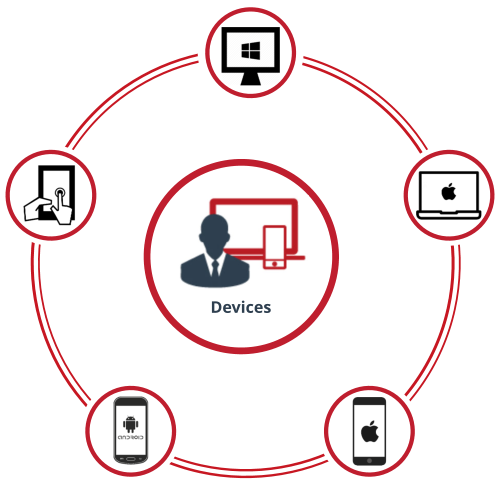
Unified Authentication Experience
Multi-factor authentication requires users to provide multiple credentials in the login process. It is inevitably more complex and time consuming than password only authentication. Typically, users often need to access different types of remote resources, services and applications, from various types of devices. For instance, you may need to connect to your corporate network remotely via VPN from your laptop, and you might also need to access your business emails from your smart phones. Therefore, the user experience in the multi-factor authentication (MFA) process is very important. A successful MFA product must provide an excellent user experience in such way that users do not see multi-factor authentication being inconvenient to use, or even reducing their productivity.
Unified Multi-Factor Authentication Platform
|
|
Adaptive Authentication |
DualShield MFA platform includes a powerful risk engine that uses machine learning to evaluate the risk level of every login request in real time. It takes context into account, including user’s Geo location, IP addresses, network location, device information and time of day. Based on the risk score, a login request can be either blocked or escalated to a higher level of MFA process.
|
|
Single Sign-On (SSO) |
DualShield platform includes a SAML-based SSO server that enables users to sign on once then access multiple web and cloud applications without additional logins. It also supports desktop to web/cloud single sign-on by leveraging Microsoft’s Integrated Windows Authentication.
|
|
Password Reset |
DualShield platform includes a secure, web-based self-service portal that enables users to remotely manage, change, reset their AD passwords, and to unlock their AD accounts. It can send password expiry notifications and securely automate the end-user password resets and account unlocks with SMS/E-mail verification code and/or security questions.
|
|
Identity & Access Control |
DualShield streamlines user management by integrating with existing user directory, such as LDAP or Microsoft Active Directory. Using a set of powerful rules, an enterprise is able to enforce intelligent access policies based on user geo location, ip address, network location, device information and time.
|
|
MFA Policy Engine |
DualShield platform includes a powerful and flexible policy engine that allows you to customise the system to your exact requirements. For instance, you can determine what types of authentication methods are appropriate for any given user and/or for any given application.
|
|
Audit, Alert & Report |
DualShield logs all events and activities that can be utilized as an auditing, accounting and monitoring tool, and also used to generate reports to meet compliance requirements or assess cyber threats. Furthermore, administrators can be alerted in real time on important or critical events and activities by email or SMS messages.