- Products
- Solutions
- Authenticators
- SaaS
- Compliance
- Services
- Resources

There is no doubt that BYOD has been widely accepted in corporate workplaces. A recent study by Cisco showed that 95% of organizations use BYOD in some form or another. This is an overwhelming statistic that shows BYOD has reached well beyond critical mass.
At the beginning of the BYOD movement, organisations simply forbid users to access corporate resources with personally owned, unmanaged devices. Eventually, in order to increase productivity and satisfaction of mobile workers, lower device costs for businesses, organisations started to embrace BYOD and allow employee owned devices access to corporate networks. Once these devices are allowed to access corporate networks, they consequentially bring a great number of risks including mobile malware, IP theft and data loss. Given that today, 95% of organizations allow BYOD devices, the threat and risk to corporate network, data and applications continues to grow exponentially.
The common security solution to attempt to solve the BYOD risk problem is Mobile Device Management (MDM). MDM appeared initially to be the killer application needed to make BYOD safe for the access to corporate network. It offered the hope that BYOD devices could meet corporate policies, allowing IT groups to enforce configuration standards and maintain compliance. While the MDM solution is important, MDM focuses on devices only. This approach falls short in the age when people are increasingly mobile too. Users can move between laptops, tablets, and smartphones from any place and at any time, while wanting a consistent experience. MDM solutions require that users give up control of their devices in order to access corporate applications, therefore,it also fails when applications must be extended to business partners and consumers who do not want organizations controlling their devices.
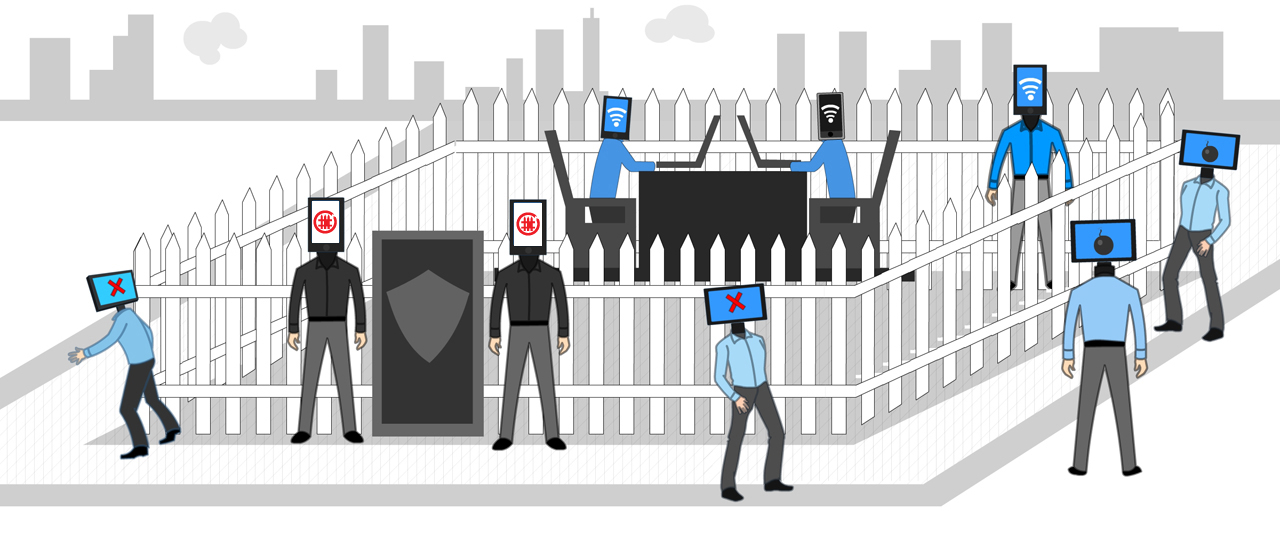
This means that no matter how much security, process and policy are in place to manage and control personally owned devices, the weakest link may very well be in the identity of the owner of the personal devices.In order to provide real-time visibility and control over smartphones, tablets and laptops connecting to corporate networks and to keep corporate networks safe from data loss and malicious threats, only trusted devices owned by trusted users should be allowed to connect to corporate networks. In other words, both the device and the owner of the devices should be authenticated and verified before the connection to the network is allowed and access to the network resources is granted.
Deepnet Security is pioneering this space with a world-first wireless Network Access Control (NAC) system empowered by Multi-Factor Authentication (MFA), Deepnet DualFence, that gives IT security managers an easy way to reduce BYOD risks. Deepnet DualFence verifies the identity of the connecting mobile devices as well as the identity of their users,provides real-time visibility of mobile devices connected to your network, controls the network access of those devices, and keep corporate networks safe from data loss and malicious threats.
Once the identity of both the device and its user are successfully verified, through two-factor authentication, Deepnet DualFence automatically enforces access rights, roles, privileges and policies within the network. If you wish to ban all guests and unknown mobile devices from your network, Deepnet DualFence can do that. If you wish to allow guests and their wireless devices to access the Internet, Deepnet DualFence can do that too.
Key Features:
Virtual Appliance
DualFence is provided as a single virtual appliance. No software to install, simple to configure. Built-in integration lets you leverage your existing infrastructure including wireless access point, routers, switches, DNS & DHCP servers and user directory.Built-In RADIUS
DualFence is an extended module in the Deepnet DualShield unified security platform which includes a built-in RADIUS server.Wireless Integration
DualFence integrates perfectly with wireless networks through the built-in RADIUS server which supports 802.1X protocol. Mixing access points (AP) vendors and wireless controllers is supported.Guest Access
DualFence’s automated guest registration process allows guests to access your network without compromising your internal network security. DualFence includes several guest registration options allowing you tailor the guest admission process to your organization’s needs.Two-Factor Authentication
Empowered with Two-Factor Authentication, DualFence allows employees to access your internal corporate network and resources while preserving security. Flexible authentication methods provide security without compromising user’s experience. Flexible policies allow full or limited network access based on user name, device type, and security posture.
